Software list
GnuPG is a complete and free implementation of the OpenPGP standard as defined by RFC4880 (also known as PGP).GnuPG allows you to encrypt and sign your data and communications; it features a versatile key management system, along with access modules for all kinds of public key directories. Free download GPG Suite GPG Suite for Mac OS X. GPG Suite - One simple package with everything you need, to protect your emails and files.
This is the complete list of software we know to work or once used towork with GnuPG. The header line indicates the supported operatingsystems and the type of the software:
- GUI
- A graphical user interface for GnuPG
- MUA
- A Mail User Agent (mail program) or a Plugin for MUA
- CHAT
- A chat client
- INST
- An installer package
- LIB
- Software to help writing programs with GnuPG support.
- SRV
- Software for use on servers.
- MISC
- Other types of software
The flag Active indicates that we know that this software isactively maintained. Obsolete mean that the software is not anymoreuseful.
Claws Mail [Unix, Windows] MUA Active
Is a very nice GTK+ based MUA with full support for GnuPG.
Cryptophane [Windows] GUI
Cryptophane is an easy-to-use application for MS Windows. It allowsusers to encrypt, sign, decrypt, and perform key maintenance withouthaving to deal with GnuPG's command-line interface.
EGD [Unix] MISC Obsolete
Unices without a /dev/random should download and installthis Entropy Gathering Daemon.
enigform [Unix,Windows,OSX] MISC
Mozilla Firefox extension for HTTP+OpenPGP support(see mod_auth_openpgp). Blackmagic media express free download for mac.
Enigmail [Unix, Windows, OSX] MUA Active
EudoraGPG [Windows] MUA
Is a plugin for the proprietary Eudora MUA.
Evolution [Unix] MUA Active
Is a catch all MUA application for the GNOME desktop.
exmh [Unix] MUA
ez-pine-gpg [Unix] MUA
ez-pine-gpg is a set of scripts that allows beginners and experts touse gpg with Pine. There are plenty of other applications that allowgpg to be used with Pine: this one is intended to be the best, sinceit merges intuitive use with powerful features. The result is anapplication that's not only fast and secure, but also perfect fornovices and power-users alike.
Gabber [Unix] CHAT

Gabber is a Free and Open Source GNOME client for an instant messagingsystem called Jabber (XMPP). Jabber is a Free and Open Source distributedinstant messaging system. It does not rely on a single server, and theprotocol is well documented. Jabber allows communication with manydifferent instant messaging systems, including ICQ and AIM.
Gajim [Unix] CHAT Active
The goal of Gajim is to provide a full featured and easy to use Jabberclient. Gajim works nicely with GNOME, but does not require it torun. It is released under the GNU General Public License.
GNU Anubis [Unix] MUA
Is an outgoing mail processor, and an SMTP tunnel between the MUA andthe MTA. It strongly uses the GnuPG via the GPGME interface. With thisGNU tool you can encrypt or sign an outgoing mail on-the-fly.
GNUmail.app [Unix] MUA Active
GnuPG Shell [Unix] GUI
GnuPG Shell is a cross-platform graphical frontend for GnuPG.
gnupg-for-java [Unix,Windows,OSX] LIB
GPA [Unix, Windows] GUI Active
Aims to be the standard GnuPG graphical frontend. GPA is hosted onthis site. The Windows version is part of Gpg4win.
gpg_encrypt [Unix] SRV
gpg_encrypt() is a PHP function that will allow you to easily useGnuPG to encrypt data to your public PGP key and mail that encrypteddata to yourself, where it can be securely decrypted with your privatekey. This is designed primarily for use with web-based forms but canbe used to encrypt any data.
gpg_mail [Unix] SRV
This script is able to encode/sign emails in an automaticfashion. There is also a mirror site available.
Gpg4win [Windows] INST Active
Gpg4win is an installer package for Windows with computer programs andhandbooks for email and file encryption.
GPGMail [OSX] MUA Active
Is a mail program for MAC OS X. Note that only the source code isdelivered without charge; a binary version requires a paidsubscription.
GPGME [Unix,Windows,OSX] LIB Active
GnuPG Made Easy is the standard library for applications to accessmost GnuPG functions.
GpgOL [Windows] MUA Active
A plug-in for the Windows version of Microsoft Outlook.It is part of Gpg4win.
GPGrelay [Windows] MUA
Is a Windows program which can be used to use GnuPG with all MUAs.
GPGTools [OSX] INST Active
GPGTools is an installer package for Mac OS X. It integrates allrequired modules for easy use of GnuPG on this OS. Note that only thesource code is delivered without charge; a binary version requires apaid subscription.
Jaro Mail [Unix,OSX] MUA
Jaro Mail is an integrated suite of interoperable tools to managee-mail communication in a private and efficient way, without relyingtoo much on on-line services, in fact encouraging users to store theiremail locally.
Keylookup [Unix] MISC
KGpg [Unix] GUI
Is a KDE frontend for GnuPG.
KMail [Unix] MUA Active
kuvert [Unix] MUA
This frontend is for GnuPG and old-style pgp2. It works slightlysimilar to Raph Levien's premail: it sits between MUA and MTA anddecides based on the keyring contents whether to sign, sign/encrypt orleave an email as it is. kuvert is unix-only and designed to work foroutbound emails only. It's a daemon tool and requires some form ofpassphrase cache. kuvert has been around (under earlier names) sinceabout 1996.
MacGPG, MacGPG2 [OSX] MISC
The MacGPG project has information on using GnuPG on OS-X.
MagicPGP [Unix] MUA
Is yet another set of scripts to use GnuPG with Pine.
Mailcrypt [Unix] MUA Obsolete
For Emacs. You may need the latest patches until there is a newrelease of Mailcrypt.
Mew [Unix] MUA
Miranda ICQ [Unix] CHAT
Has support for GnuPG.
mod_auth_openpgp [Unix] SRV
Apache module for HTTP+OpenPGP support(see also Enigform).
Mutt [Unix] MUA Active
Is an advanced non-graphical MUA with complete MIME and GnuPG/PGPsupport.
NSBD [Unix] MISC
OpenPGP Webmail [Unix] SRV
Is a web based mailer to send encrypted messages.
PGG [Unix] MUA
PGG is a complete PGP signing/encrypting solution provided fromscratch by the Gnus development team. It deserves the same thanmailcrypt but it has also native MIME support whereas mailcrypt doesnot. There is no PGG homepage at the moment, sorry.
PGPdump Web interface [All] MISC
Gpg Suite Mac Os X
pgpenvelope [Unix] MUA
Is a Pine and procmail filter which allows one to process messageswith GnuPG.
pgpgpg [Unix] MISC
Is a comandline wrapper tool to allow the use of scripts written forPGP with GnuPG.

PGPHTML [Unix] SRV
Pinentry [Unix,Windows,OSX] MISC Active
Secure PinEntry Dialog. This is required by GnuPG-2 and part of allinstallers.
Python GnuPGInterface [Unix] GUI
PSI [Unix, Windows] CHAT Active
Psi is a free and crossplatform client for connecting to the Jabbernetwork. It supports multiple accounts, group chat, Unicode, andstrong security (TLS and GnuPG).
Scribe [Unix, Windows] MUA
Scribe is a small and fast email client that lets you send, receiveand manage email without fuss. Scribe comes with a plugin that callsGnuPG.
Securemail [Unix] SRV
Seahorse [Unix] GUI
Is a GNOME frontend for GnuPG.
Soupermail [Unix] SRV
Squirrelmail Plugin [Unix] SRV
A gpg plugin for the popular Squirrelmail web mail server.
Sylpheed [Unix] MUA
Is a very nice GTK+ based MUA with full support for GnuPG.
Tkabber [Unix] CHAT
Tkabber is a free client for an instant messaging system calledJabber (aka XMPP). It is written in Tcl/Tk and supports many features likesupport of unicode, ssl support, http proxy, file transfers andsupport of multi-user conference protocol.
Topal [Unix] MUA
wija [Unix, Windows, OSX] CHAT
wija is a free and cross-platform Jabber/XMPP client written in Java,with built-in GnuPG key rings management GUI. Its extended protocolsallow users to encrypt chat and multi-user chat as well asencrypting/signing messages and signing presence of the user. It ismultilingual and runs on GNU/Linux, Mac OS X and Windows.
WinGPG [Windows] GUI
WinGPG is a tray-based classical Windows application, Windows NTExplorer shell extension, and a classic GPGv2 distribution (it usesthe cryptography from the official site without making anymodifications).
XAP [Unix] GUI
XFmail [Unix] MUA
Works with GnuPG.
- Installing Software
- Generating GPG keys
- Using your newly created GPG key with Cerb
- Publishing your public key
To automatically decrypt a received encrypted message in Cerb, you need to have the corresponding private key in your keyring. If you receive an encrypted message that can’t be decrypted, Cerb will leave the encrypted content as an attachment on the message that you can decrypt offline. This is the most secure option, but the content of the message won’t be readable or searchable within Cerb.
If you want automatic decryption of messages, you need to consider the security implications of leaving your private key on the server. At the minimum, we recommend that you create a subkey following the steps documented here so you won’t be storing your master key on the server.
If you are running Linux or Windows, the instructions below can be used with some modifications. We will release platform specific guides for them in the future.
Install Homebrew
This guide assumes you use Homebrew to install packages on your Mac. If that isn’t the case, Homebrew is a package manager (similar to RPM or deb on Linux) that makesit easy to install software on your Mac. Please visit http://brew.sh and follow the instructions to install it.
Install GPG
Gpg Mac Os X Command Line
To generate your keys, you need to install GnuPG (aka GPG). GPG is a free software alternative to the closed source commercial PGP. To install GPG with Homebrew, it’s as simple as:
Enable GUI for passphrase entry
You might have noticed we installed two things, GPG and something called pinentry-mac. Pinentry-mac is a tool which prompts with a native dialog box for your GPG key passphrase and alsoallows you to store the password in your Mac’s Keychain. As Homebrew helpfully prompted after installing pinentry-mac, we now need to enable it.
While pinentry-mac allows you to save your passphrase, in the interest of security you shouldn't. Best product key finder for mac.
To enable it, you first need to run GPG to have it setup its directory structure.
This can be accomplished by simply running:
You don’t have any keys in your keyring yet. Let’s fix that in a moment. After getting GPG to create its directory structure, we now need to enable pinentry-mac.We do this by editing the file $HOME/.gnupg/gpg-agent.conf. You can use VIM (or a text editor of your choice) as shown below:
Or you can accomplish the same thing by running this:
After setting pinentry-mac up, when GPG prompts you for a passphrase, you’ll see something like this:
Now that you have GPG installed, we need to generate the keys which are used for encrypted email. Following best practices, we will be generating a master key and then a subkey for usage by Cerb.This way if your subkey is ever compromised, it’s a simple process to revoke and replace it. The master key you should protect as you would your bank password.
Generate master key
We will be removing the Sign and Encrypt capabilities from the master key forcing usage of subkeys for those operations. This limits the damage that can be done if the master key is ever compromised.
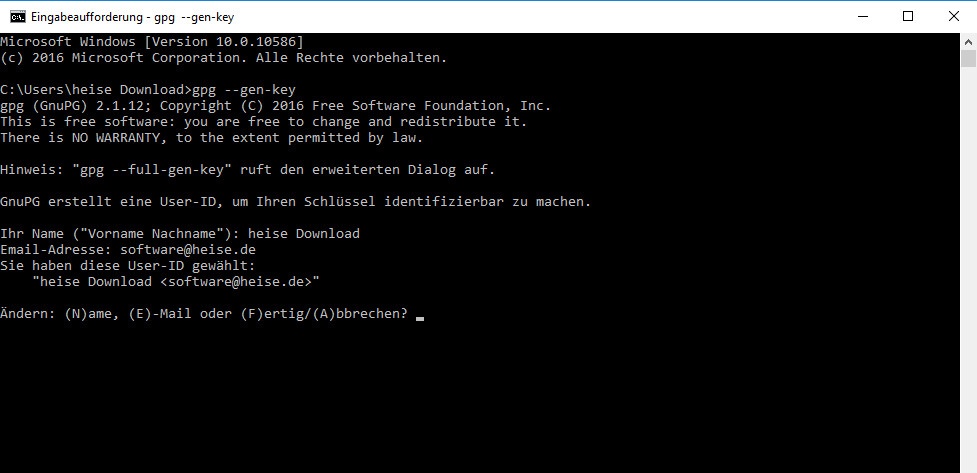
To generate the master key, follow these steps:
- To start the process:
- When prompted for what kind of key, pick option:
(8) RSA (set your own capabilities). - Next you want to toggle off the sign and encrypt capabilities from the key.
- When prompted for capabilities, type
sand hit enter to toggle off the Sign capability. - Next type
eand hit enter to toggle off the Encrypt capability. - Confirm that the current allowed actions only lists
Certify, then typeqand hit enter to finish setting capabilities.
- When prompted for capabilities, type
- Now you are prompted for how long the RSA key should be. Type
4096to set the highest security that GPG currently supports. - For expiration, we suggest picking
0so the key doesn’t expire. - Now GPG needs to know who this key is for. For the Real Name, we suggest picking the same “friendly name” you use for outgoing email from Cerb.
- Next provide the email address you want to use for receiving encrypted email.
- We will reference this email as
YOUR@EMAIL.comfor the remainder of this guide.
- We will reference this email as
- If you’d like to enter a comment for the key, you can do so next. Otherwise hit enter to skip it.
- If everything looks good at this point, hit
ofor Okay. - You will now be prompted for your master key passphrase. Please ensure this is a secure password that you have not used anywhere else.
If you are unsure about any of the above, the screenshot below shows the entire key creation process.
Set secure preferences on key
Now that your master key is created, we want to set the preferences on the key to ensure current best practices.
- To edit the key, you need to run:
- Paste in the following to set the preferences:
- Type
yto confirm. - Type
saveto save and exit.
Add GPG subkey for Cerb
Now that you have your master key, we need to create the subkey used for Encrypt and Sign in Cerb. The process for this is similar to what you have already done before.
- To add the subkey, you need to first run:
- At the prompt, type
addkey. - Choose option:
(8) RSA (set your own capabilities)as before. - Unlike before, the capabilities are already set the way we want (“Sign Encrypt”), so type
qto finish capability selection. - Type
4096as previously done for the keysize. - Next, we suggest using
0for no expiration as before. - Confirm
yat the next two prompts. - After entering your passphrase, your subkey is now created.
- Type
saveto quit and exit.
Export keys for safe storage
This step is critical to the safety of your GPG keys. If you don't do this, your keys could be forever lost or worse.
To export your private key, run the following replacing YOUR@EMAIL.com in both places with your email address used when creating the key.
We will also export the public key to keep with the private key:
Next, we will create a revocation certificate for the key in case it is ever compromised:
Follow the prompts to create the revocation certificate. For reason, we suggest 1 = Key has been compromised and you can hit enter on the description line (it’s not needed).
Now that we have these three files created, back them up on a USB drive and put in a very safe place (safety deposit box is a common suggestion).After copying them to a USB drive, we highly recommend deleting the file ending in .private.gpg-key and .gpg-revocation-certificate immediately.You do not need to delete the file ending in .public.gpg-key as we will use it later.
Remove passphrase for using with Cerb
Now that the master key is preserved safely, we need to remove the passphrase for using your GPG key with Cerb.This isn’t a standard process, so GPG is persistent in making sure it’s what you really want to do.
- Edit the key as before via:
- At the prompt, type
passwd. - You will first be prompted for your existing passphrase.
- When prompted for a new passphrase, hit enter.
- When prompted, pick “Yes, protection is not needed”.
- The above two steps repeat multiple times, keep repeating until they stop asking.
- Type
quitat the prompt to finish.
The screenshots below illustrate the process and the prompts you must acknowledge.
Delete master key from local keyring
Now that your GPG keys are backed up and currently not secured by a password, we need to delete the master key locally for security reasons.
- First we need to get the keygrip for the master key so we know what to delete:
- Take note of the first
Keygrip =line in the output, consult the below screenshot as needed.- Now that you have the key grip, you need to use it to delete the master key locally from your keyring:
- Finally we want to make sure it’s really gone:
As shown in the below screenshot, make sure that there is a # after sec at the beginning of the 3rd line. This indicates that the master key is offline as it should be.
Export subkey for using with Cerb
With all that out of the way, we need to export the subkey we created to use it with Cerb. Run this in a Terminal to export the subkey:
You will use the contents of this file to enable Cerb to decrypt encrypted email sent to it in the next step.
There are two methods for importing your subkey into Cerb. We recommend importing it via your browser for simplicity.
Importing via your browser
Cerb 8.1.0 doesn’t have a direct way to add GPG private keys, but thankfully GPG treats them the same for purposes of importing.
- Navigate to Search » Public Keys.
- Add a new record by clicking on the (+) above the worklist.
- For the name, enter in
YOUR@EMAIL.com private subkeyor similar. - Paste in the contents of the exported private subkey as generated previously.
Skip over the next step and jump ahead to Publishing your public key.
Importing via command line
To import via command line, you first need to connect via SSH to the server where Cerb is hosted. If you are a Cerb Cloud customer,this isn’t possible so you will need to use the above instructions to do it via your browser.
- Change into the directory where you have Cerb installed.
- Tell GPG where to find the keystore used by Cerb:
- Check to see if you have existing private keys:
- Import the subkey you created previously:
- Verify the key exists now and that the master key is offline as before:
Now that you have Cerb setup to receive encrypted email, you need to tell the world about your public key so they can encrypt emails to you.There are a number of different public key servers commonly used, so we recommend submitting to them all for coverage.
You’ll need your public key to do this, so if you don’t still have it from the Export keys for safe storage step earlier, you can re-export it now with:
Using Keybase
We highly recommend using a service like Keybase, which not only verifies the email address of a public key, but also allows the key ownerto prove their identity by verifying ownership of domain names, profiles on various services (e.g. Twitter, GitHub), Bitcoin wallets, etc.
As the setup is a bit more involved than the below three options and subject to change, we recommend visitinghttps://keybase.io/ and following their guide.
You can also import public keys from Keybase right into Cerb.
Using MIT’s public key server
MIT’s public key server is accessible at https://pgp.mit.edu. The screenshot below shows where to submit your public key:
Using Symantec’s public key server
Symantec’s public key server is accessible at https://keyserver.pgp.com.
To submit a key to them, visit the Submit Key page and upload your key there as shown in the screenshot below.
Using Key-server.io’s public key server
Key-server.io’s public key server is accessible at http://pgp.key-server.io. The screenshot below shows where to submit your public key:
Gpg-agent Mac Os X
Links on how to setup setup storage of your private key on a popular hardware device:
